User roles and permissions
There are three default roles
Host / Editorial Staff
Programme Manager
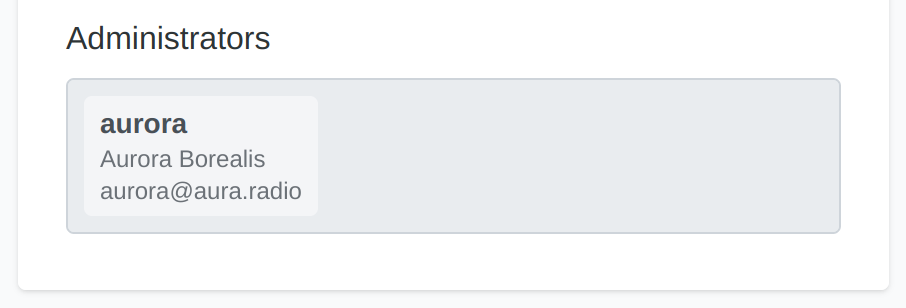
Radio Station Administrator
To learn more about these roles, check the user and host profile page.
In the radio administration these roles are realized using groups and an assigned set of permissions. But any of these permissions can also be assigned individually to user accounts.
The Host / Editorial Staff role is provided in two flavors, in form of a host Host and Host+ group. This allows administrators to get an impression on different permission capabilities more quickly. When finalizing the radio station configuration, decide for one of these Host groups and modify individual permissions to your organizational needs.
Public visibility of data
Whenever editing any data, keep in mind, that almost all data is visible via public APIs. All the data is read-only for non authenticated users. Basically the API provides all data which is typically also visible on radio station websites.
Additionally, this also includes metadata like when and by whom a record was created or updated last.
The only exceptions are those fields, which are only visible internally and only editable by certain roles:
Area |
Field |
Visible only to these roles |
|---|---|---|
user |
first name |
All authenticated users |
user |
last name |
All authenticated users |
user |
All authenticated users |
|
host |
All authenticated users |
|
show |
All authenticated users |
|
show |
internal_note |
Programme managers |
Open data principle vs. user privacy
As advocates for open data, we’re all about transparency, just like community radio stations. But remember, always follow the law in your area. For example, in the European Union (GDPR), users need to agree before you share their personal data. So, be sure to get their written consent first.
Secure storage of user passwords
We want to assert, that passwords are only stored in hashed form and are therefore not even visible to administrators. They are never exposed by API, since authentication is performed using OpenID.
Groups and their default permissions
Beside the default read-access, the groups are pre-configured with these permission assignments:
Area |
Field |
Host |
Host+ |
Programme Manager |
|---|---|---|---|---|
show |
name |
|
||
show |
slug |
|
||
show |
short description |
|
|
|
show |
description |
|
|
|
show |
logo |
|
|
|
show |
image |
|
|
|
show |
categories |
|
||
show |
topics |
|
||
show |
music genres |
|
||
show |
languages |
|
||
show |
type |
|
||
show |
|
|
||
show |
links |
|
|
|
show |
hosts / editorial staff |
|
|
|
show |
administrators |
|
||
show |
funding category |
|
||
show |
cba id |
|
||
show |
predecessor |
|
||
show |
internal_note |
no read access |
no read access |
|
show |
is active |
|
||
show |
default media source |
|
|
|
schedule |
default media source |
|
|
|
episode |
title |
|
|
|
episode |
summary |
|
|
|
episode |
content |
|
|
|
episode |
image |
|
|
|
episode |
contributors |
|
|
|
episode |
topics |
|
||
episode |
languages |
|
|
|
episode |
tags |
|
|
|
episode |
links |
|
|
|
media-source |
file |
|
|
|
media-source |
line |
|
|
|
media-source |
stream |
|
|
|
media-source |
import |
|
|
|
host |
name |
|
|
|
host |
biography |
|
|
|
host |
|
|
To serve the overview, permission strings in the table are simplified. When looking up the actual
permission string, take the permission verb and combine it with the field name in format
Can {verb} {field}. For example Can edit music genres is the permission string you will find
in the permission assignment interface.
All cells without a permission string represent read-only access, except the ones marked with no read access.
Each group also holds wildcard permission assignments like add episode, change episode,
delete episode and view episode which is not visible here. These are required for properly
granting access to data by inheriting global permissions. Some are required for permissions
through ownership (see next chapter). Generally you should not edit these assignments.
Permissions through ownership
Permissions through ownership only affects the Host and Host+ roles, since Programme Managers have all relevant permissions to manage all shows and profiles.
Ownership of shows and episodes
Users which are assigned as Show Admins in the show settings, automatically have the permissions to list and edit their own shows, according to the assigned role (Host, Host+, or individual permissions). The permissions listed in the table, only grant users editing rights for shows they are actually owning.
Ownership permissions on shows and their episodes is granted by having these wildcard permissions assigned:
Can change show
Can change episode
Ownership of host profiles
In case of the host profile, only the owner can edit the fields, they have permissions on. Here ownership is represented by a relation between user and the host profile.
Additionally editorial staff members need the ability to assign guests to certain episodes (contributors). To do so, they often need to create host profiles on-the-fly.
Ownership permissions on host profiles is granted by having these wildcard permissions assigned:
Can change host
Assign roles and permissions
Read here, to learn on how to assign roles and permissions: